Issue#14
Welcome to 2006
- Technology Takeaway (r), a service of Moskowitz, inc.
- Just one LOONG tip: Creating a Bulletproof desktop with the Shared Computer Toolkit.
- Get a signed copy of...
- my GP book: Group Policy, Profiles and IntelliMirror
- my Windows & Linux Integration book
- Free, Free, Free speeches by Jeremy
- By popular demand: The three-day less-intensive GP Course in PA
- Upcoming Public two-day GP Classes for 2005 / 2006
- What's new from GPanswers.com
- What's new from Microsoft
- Subscribe, Unsubscribe, and Usage Information
Moskowitz, inc. and www.GPanswers.com
This issue, we tackle something that's near and dear to me: Desktop Lockdown. It certainly feels as if all the Group Policy settings available to us would allow us full control over our desktops. But, there's something missing. In this issue, we'll explore the Shared Computer Toolkit which makes your Ultimate Desktop Smackdown vision possible.
After we talk about this, I'll give you an update on my 2006 Group Policy Class Schedule and show you some cool new features we've added to GPanswers.com.
Newsletter Sponsored by: DesktopStandard
Built-in Windows security management features simply don't give you enough granular access. As a result, administrators run applications with full administrative access - even if it is not required. This exposes the network to unnecessary security risks like viruses and spyware.
DesktopStandard's PolicyMaker line of Group Policy Extensions solves this problem with Application Security policy. Click the link to learn how you can empower your users to be more secure today.
Technology Takeaway®, a service of Moskowitz, inc.
Bulletproofing your shared desktop -- with the shared computer toolkit
One of the top requests I get at GPanswers.com is how to take machines and âlock them down.â People want ways to ensure their machines canât be broken by Joe User or Harry Badguy. The âout of the boxâ Group Policy settings can go a long way towards solving this common conundrum. But the settings in the box can only take you so far.
The situations involving computer lockdown can get complexâfast. You might not even know the people who are walking up to the machine, but you still have to give them some portion of your network resources like Internet browsing, file viewing, or printing.
You would typically find computers like these in places like universities, airports, hotels, community centers, museums, kiosk stands, and conference centers . So, these arenât the kinds of machines that your typical business users utilize day to day; these are the kinds of machines where people need sporadic access, and they are people that you may or may not trust. And by ânot trustâ I mean theyâre potentially downloading infectious junk off the Internet. They may be inadvertently adding spywareâor worse, theyâre really out to get you and are going out of their way to try to damage your public-access PC.
What you need is a way to restrict anything from being written to the Windows partition. You need a way to trap the bad stuff, but keep the good stuffâlike critical Windows updates and antivirus updates. You need a way to lock down Windows so itâs much harder to get to the under-the-hood Windows stuff, like the C:Windows directory. And you need a way for new users to get a guaranteed profile, so youâre dictating their experience, not fighting to clean up after them. However, if youâre dreaming a little bit, you might also want to manage exceptions. That is, you might want to have a known or trusted user use this shared PC for some specific task, and to make sure that their data and settings stick around.
What you need is the Shared Computer Toolkit, or SCT. While the SCT can be many things to many people, itâs not specifically meant to be loaded on every desktop to restrict the actions of day-to-day employees (though Iâm sure some enterprising geeks will attempt to roll it out corporation-wide). Itâs also not really meant as a âparental controlâ device either, though there might be some attributes of the SCT which might be useful there.
Requirements
To use the SCT, you need a Windows XP/SP2 machine with at least 1GB of unallocated space (though having 10% of the hard drive unallocated is recommended.) This unallocated space will be converted into a special âprotection partitionâ by the SCT Additionally, you might want a second âDataâ partition to store persistent data from trusted users to whom you specifically grant access. For instance, if someone uses this machine for their daily work, you might want them to be able to save Word documents on this additional partition.
One of the tricks is getting a machine which already runs Windows XP/SP2 and carving out some unallocated space. Typically, when Windows is installed the entirety of the hard drive is used, therefore there is no unallocated space. However, any repartitioning tool will make it possible, such as Symantec Partition Magic, Terrabyte BootIt Next Generation, or Acronis Partition Manager (part of the Acronis Disk Director Suite). The Microsoft documentation for the SCT specifically mentions the first two, but I already own the Acronis product and used that one with no problems.
There are two main ways to use the SCT: when machines are not joined to the domain, or when machines are joined to the domain. Weâll examine both scenarios here.
Getting Started with the SCT
After youâve re-partitioned the machine, youâll take the following steps to use the SCT:
- Install all the applications that you want to make available on the shared computer.
- Remove Windows components that you donât want people to use (or would be potentially dangerous for people to use) like IIS, or Outlook Express.
- Install the SCT after installing the required User Profile Hive Cleanup Service (UPHClean).
- Configure the SCT.
Once SCT has been configured, its goal is to keep your computer as clean as the day you installed it. Therefore, be careful that youâre not actually loading âjunkâ on your shared computer as youâre preparing it for use.
At the heart of the SCT is the Windows Disk Protection service, or WDP. The goal of WDP is to âtrapâ writes to the Windows system volume, and temporarily store them on the Protection Partition so the bad guys canât actually do any permanent damage to the real Windows partition. Once the session is over, so is any accompanying potential damage.
However, the SCTs cannot prevent certain attacks from being attempted. Even though the SCT will help you lock out Windows functions like Explorer, that doesnât mean an application youâve installed and made available for use doesnât have Explorer-like capabilities. For instance, many applications allow you to browse the contents of the hard drive when youâre in their File | Open dialog boxes. Again, the SCT will ultimately prevent the disruption of Windows because of the WDPâthat is, the WDP ultimately discards any writes to the system volume. However, it is incapable of preventing this kind of âpoking aroundâ attack if your application lets them poke around.
To download the SCT, go to Microsoftâs website here. What I like most about the website is the opening graphic where three kids are ostensibly âlearningâ on the machine. However, what we really know is that theyâre right-clicking over your favorite disk partition and selecting âFormat.â With the SCT, youâll be protected from rascals of all age groups.
The SCT installation is Wizard-driven, and is a snap to use. However, it requires an additional package, called the User Profile Hive Cleanup Service, or UPHClean. UPHClean is popular with Terminal Services administrators whose users have difficulties logging off Terminal Services and having their User Profiles setting saved. Itâs interesting to note that UPHClean is now a required component for this SCT. It would have been nice if the SCT installation didnât make you download it separately, but (since you need it anyway) simply made it part of the SCT installation.
Configuring the SCT in 8 Easy Steps
Once SCT has been installed, configuring it is made easier with a Getting Started page (seen in Figure 1), which steps you though the configuration process.
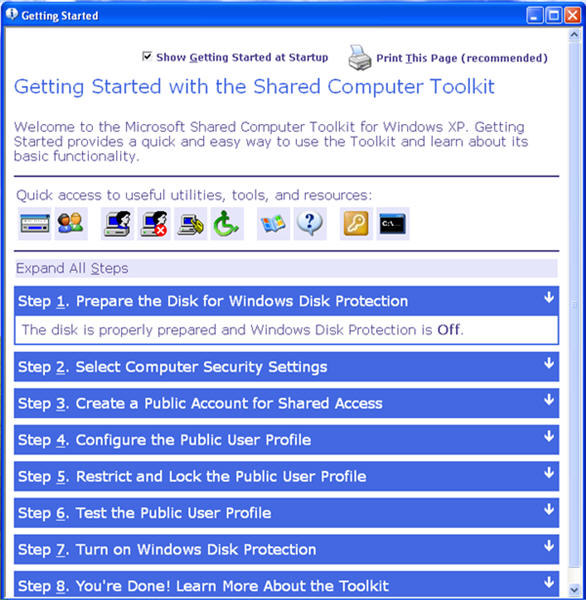
Figure 1: The SCT Getting Started page is a like a guided setup (click on figure to enlarge)
After the Getting Started guide appears, itâs easy to walk step-by-step through the process. The second step, as seen in Figure 2, is mostly configuring security-related Group Policy settings which are being set within the local GPO. In most cases, youâll want to make sure all boxes are checkmarked.
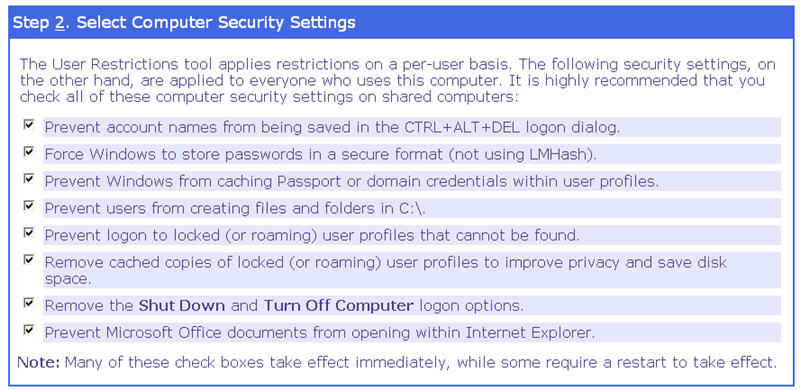
Figure 2: Step 2 mostly deals with security-related Group Policy settings (click on figure to enlarge)
Step 3 simply has you create a new local user and give it a name of your choosing, such as Public.
Step 4 has you actually configure the user account the way you want: configure the desktop wallpaper, accept first-time run settings and license agreements (for programs such as Windows Media Player, Microsoft Office, and Acrobat Reader), add printers, etc. Whichever way you configure this profile is how all public users on this machine will see it.
Step 5 has you select the Public profile and locking down some additional settings, as seen in Figure 3. There are too many options to delve into right here. Thankfully, the recommended settings are all located in one place and can be selected with one Checkboxwhich highlights all of them. Defaults here include the restriction on running applications from USB thumb drives, restricting the running of system tools (such as regedit.exe), and preventing users from right-clicking within Internet Explorer.
Optional Restrictions, such as âRemove CD and DVD burning featuresâ and âPrevent printing from Internet Explorerâ are welcome additions.

Figure 3: Itâs easy to administer perform the kinds of restrictions you want to apply to all users (click on figure to enlarge)
Step 6 has you actually testing the Public profile before you go into lockdown mode. This enables you to see what the user will see, but still makes it easy for you to go back and make changes in the SCT Getting Started steps.
Step 7 contains the secret sauceâthe Windows Disk Protection service, which requires a reboot before it can be configured. Here, you can specify whether or not to retain changes made by public users, and how critical updates are handled, as you can see in Figure 4.
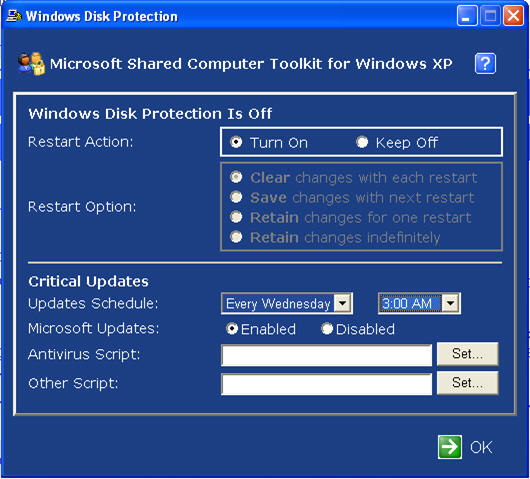
Figure 4: Once Windows Disk Protection is turned on, you can Clear, Save, or Retain changes as you see fit, as well as schedule Critical Updates, and set other options. (click on figure to enlarge)
The WDP features a very, very strong protection mechanism with four choices:
- âClear changes with each restartâ: Once this function is turned on, the system is officially protected. All historically âsensitiveâ parts of the system, such as the registry, services, even critical boot files like boot.ini and NTLDR are protected from permanent harm.
- âSave changes with next restartâ: Once the CST has been running for a while, you might realize you want to add another application to the system, or make another permanently desired change. To do this, you need to specifically select âSave changes with next restartâ and youâll have skirted around WDP this one time and integrated your changes. A quite note before this functionâs use: be sure to restart the computer before you load your new application, so as not to keep something bad or unknown. Then, once loaded, select âSave changes with next restart.â
- âRetain changes for one restartâ: If youâre adding a new application, and that application requires a reboot to finish its installation, select this option. Then, once youâre convinced youâve loaded and configured the application correctly, pick the âSave changes with next restartâ option to permanently seal in your changes.
- âRetain changes indefinitelyâ: If you want to load many applications and watch their interactions over time, you might select this option. Once youâre ready to accept your changes then select âSave changes with next restart.â If you want to back out of all changes, select âClear changes with each restart.â For example, this functionality is great for computer training centers where a new class comes in every week and you want students to have free rein over the computer. You can let them do what they want and they can restart the computer us much as they need to. At the end of the week, just clear the changes and the computer will be restored to its Monday morning state.
Another way to think about these settings is that once WDP is turned on, all changes are written to the Protection Partition (this was the previously unallocated space you carved out) until you choose âSave changes with next restartâ, and they are merged with the real partition.
Itâs likely your other corporate computers are downloading critical Windows updates from Microsoft or from WSUS by themselves (see my article in Technet Magazine about corporate WSUS settings.) However, computers using the SCT need a little TLC. That is, these computers need you to manually grab these updates. When itâs time to automatically install patches, the interactive user is logged off, and during the Critical Updates installation time, no users (other than administrators) can log on. It should be noted that when Critical Updates are downloaded, they are always written directly to the ârealâ Windows partition and not the Protection Partition. The process is quite elegant: An automatic reboot clears any potentially damaging changes users might have introduced, andthen the updates are written. This ensures that only the Critical Updates make it onto the disk.
Additional Ways to Configure the SCT
So far, the discussion has been for one standalone PCânot a domain environment. One PC is a good start, but not likely how corporations, schools, and the like will ultimately roll this out. The two additional scenarios to consider are:
- Domain-joined SCT machines, and
- Mass deployment of the SCT (domain-joined or not)
If your target SCT machine or machines are domain-joined you can, of course, go through all the steps listed above to get the job done. But that means you have to visit each and every machine to do the job. Instead, the SCT team (thankfully) rounded up their hard work and made a Group Policy ADM file which just snaps right in to the Group Policy Editor. This file (SCTSettings.adm) is located in the C:Program FilesMicrosoft Shared Computer Toolkitbin directory. This enables you to make mass changes on multiple SCT-enabled machines, as seen in Figure 5. The ADM template is a little rough around the edges and could use a little cleaning up of the Explaintext entries to be as useful as possible, but itâs a really good start.
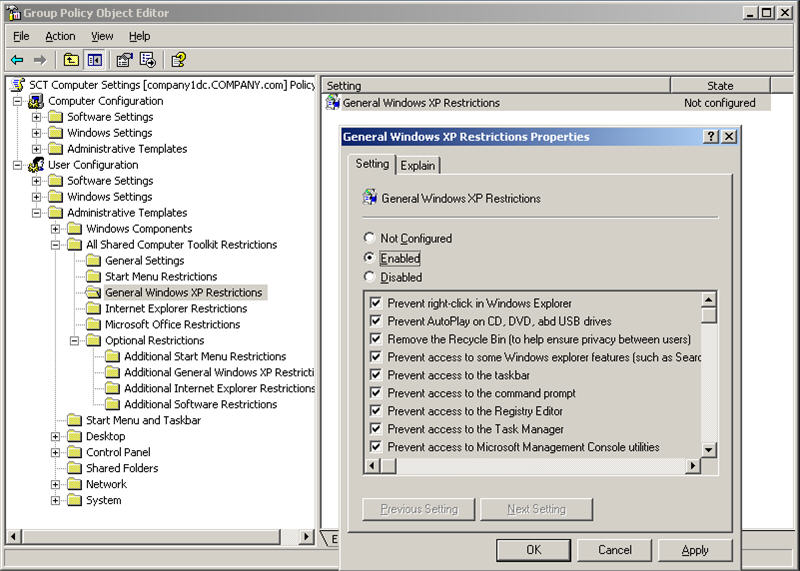
Figure 5: You can mass-implement changes to SCT-enabled machines via Group Policy (click on figure to enlarge)
There are some additional technical obstacles to overcome with domain-joined machines. For instance, how do you run around to 1,000 SCT-enabled machines and reconfigure their disk-protection settings? Thankfully, thereâs a DiskProtect.wsf provided which you can use to script the behavior of your SCT-enabled machines. You also need to manually implement the suggested Software Restriction Policy settings which prevent System Tools and unwanted programs to run. This is all very well spelled out in Chapter 10 of the Shared Computer Toolkit Handbook, which is titled âThe Shared Computer Toolkit in Domain Environments.â
The next hurdle is the mass deployment issue. That is, how do you get the SCT bits and pieces on the target machines in the first place? The suggested avenue here is to imbed the pre-installed SCT and corresponding bits inside your âGhost-styleâ or âRIPrepâ image build. Or, if you deploy âcleanâ machines, you could simply script the UHPClean and SCT installation using post-installation script commands. My first choice would be to use Group Policy Software Installation and simply assign both UHPClean and the SCT to your shared computers via Active Directory and Group Policy.
Once you have the required bits on the machines, simply use the included Group Policy ADM and .VSB files to control the computers after theyâve been deployed.
However, there are still two more hurdles to overcome. Every Windows machine must be expressly validated by Windows Genuine Advantage. This becomes a bit of a problem because each machine needs to be âtouchedâ, either by installing an IE Active Xcontrolor running an HTA application.
The last problem is, how do you remotely repartition a computerâs hard drive if you donât want to trot over to it? Remember, every SCT computer needs the required Protection Partition. If you have your own ideas of how to âmass validateâ computers via GTA or remotely repartition a computer, donât keep it a secret! Let me know and Iâll post a follow-up on GPanswers.com.
Final Outcome
Once the computers have been deployed, your users log on with the username you set; in our examples it was âPublicâ. And if you were using a domain account, you could feel free to use that as well. Once theyâre logged on, it really is a restricted, bulletproof machine as seen in Figure 6.
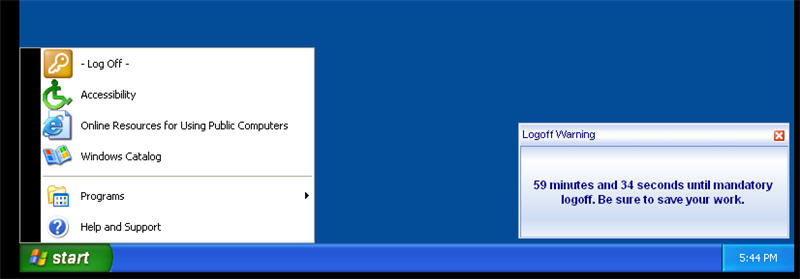
Figure 6: The final outcome of an SCT-enabled machine with restrictions enforced (click on figure to enlarge)
This is a really great tool with lots of potential uses. The tool itself as well as the documentation is well thought out, and the additional control via Group Policy is just icing on the cake for a Group Policy control freak like me.
Online support for the tool is available at Microsoftâs newsgroups, here.
Additionally, before running headlong into a real deployment using the SCT, I suggest you read the included Shared Computer Toolkit Handbook, which is well-laid-out PDF file.
For a 1.0 release, this tool really gets the job done.
SPECIAL THANKS to the Shared Computer Toolkit team at Microsoft for reviewing this article for technical accuracy. This article will appear in the July issue of Microsoft's TechNet Magazine. Consider subscribing. Click here to check out the magazine.
Get signed copies of...
Group Policy, Profiles and IntelliMirror for Windows 2003, Windows XP and Windows 2000 (THIRD EDITION)
-and-
Windows & Linux Integration: Hands on Solutions for a Mixed Environment
Do you have the new THIRD EDITION of the Group Policy book? It's got 50 new pages, fully covers XP/SP2 and Windows Server 2003/SP1, an armload of new tidbits here and there, and whole new section on the Security Configuration Wizard.
Order your signed copy today by clicking here.
Additionally available is my new title Windows & Linux Integration: Hands on Solutions for a Mixed Environment from www.WinLinAnswers.com/book.
Oh, and if you own either book, and want to say nice things on Amazon, please do so! That would be great. Thanks! You can do so here:
http://www.amazon.com/gp/product/0782144470 (GPO book)
http://www.amazon.com/gp/product/0782144284 (WinLin book)
Free, Free, Free!
Well, the price is right, even if it stinks. But it won't stink -- I promise you'll learn something, or DOUBLE your money back!
Windows & Linux: Perfect Together (Online Roundtable)
Jan 26, 2006 from 2.00 to 3.00 PM EST (11.00 to 12.00 PST) This will be a live talk with me, my co-author of my Windows/Linux Integration book (Tom Boutell) and others! The topic: Windows & Linux Integration -- so sign up and see you online! Bring your questions! Click here to register.
WSUS Architecture Crash course
Feb 10, 2006 from 12.00 to 1.00 PM EST (9.00 to 10.00 PST) Patches and updates can be a real headache to manage. Microsoft Windows Server Update Services (WSUS) is here to make your life easier. Have you implemented it yet? This is a "Power Hour" webcast with 30 minutes allotted to talk and demos and 30 minutes allotted to questions and answers. Click here to register.
By popular demand: The "Less Intensive" Group Policy course is available as a trial in Pennsylvania
Last month I debuted my new three-day "Less Intensive" format. I explained how this course was only available for PRIVATE courses.
Well, as an experiment, I'm making it available as a PUBLIC course in Newtown, PA in February 7, 8 and 9.
This course starts with a half day warm-up of Active Directory, managing users and delegating permissions. Then, we move on to the Group Policy goodies. This way, those with less Group Policy and day-to-day administration can get a bit of fundamentals before diving in to the Group Policy waters.
Public Group Policy Intensive Training and Workshop Schedule Update
I've basically lost count at this point to how many people have signed up and taken the two-day Group Policy Intensive training and workshop. Students LOVE it, and managers LOVE the results the training gives.
You BOUGHT and IMPLEMENTED Active Directory -- now DO SOMETHING with it.
So, learn to properly drive that "Ferrari" you bought by coming to a class!
Classes for first half of 2006 (lots of date changes since the last newsletter. Sorry about that.):
Feb 7, 8, 9: Newtown, PA (Three day, "less-intensive" AD/GPO course). Newtown, PA is near Trenton, Philly, and other major metro areas.
Feb 21 - 22, 2006: San Antonio (We almost have enough interested people. If you're interested, or ready to sign up, don't be a stranger! You might be that one person we need to make this class A GO.)
Feb 27 - 28, 2006: Portland, OR
Mar 2 - 3, 2006 : Atlanta, GA
Mar 15 - 16, 2006: Washington, DC
Mar 30 - 31: Sacramento, CA
Apr 20 - 21, 2006: Tulsa, OK (not Okla. City, as previously reported.)
May 15 - 16, 2006: London, England
Why THESE cities? Because people used the "Suggest a city" form at https://www.gpanswers.com/suggest and ASKED me to have classes here.
Here's hoping you'll take advantage of the opportunity!
Learn more and sign up at: https://www.gpanswers.com/workshop
(Don't forget to scroll all the way to the bottom of that page and locate your city!)
Or ... if you think you might want your own in-house training of the course (with all the personalized attention that affords), I'd love to join you onsite!
If you have even a handful of in-house people interested in the training, the course pays for itself (as you don't need to ship people offsite!). I'll even travel overseas to the U.K., other parts of Europe, or Japan -- or wherever! Have passport, will travel!
Again, while the training course isn't officially endorsed by Microsoft, the class does the have distinction of being a suggested avenue for intense Group Policy training by members of the Group Policy, Microsoft Consulting Services and Product Support Services teams at Microsoft!
For a public class, sign up online at: https://www.gpanswers.com/workshop/
For a private class, just contact me at [email protected] or call me at 302-351-8408.
Other Changes around GPanswers.com
In the last issue, I explained about our "mini-web overhaul." I'm trying to keep the new features coming so you can have the best Moskowitz,inc. / GPanswers.com / WinLinAnswers.com experience. New since last time:
- The FAQ/Tips and Tricks area has even BETTER categories, which makes things easier to search
- Did you know the GPanswers and WinLinAnswers community forums are RSS enabled?
- The RSS feed for the GPanswers.com/community room is: https://www.gpanswers.com/community/rss.php
- The RSS feed for the WinLinanswers.com/community room is: http://www.winlinanswers.com/community/rss.php
- If you're not a big fan of RSS, you can get new posts on any given forum MAILED to you. I've been waiting FOREVER for this feature. You need to enable it for any and every forum you want to "watch". When any new post appears in the forum -- you get a little email summary. This is great for the Announcements forum, or any specific technical forum to make sure you don't miss a great question, or a great answer. Click on the graphic below to see where this feature is found.
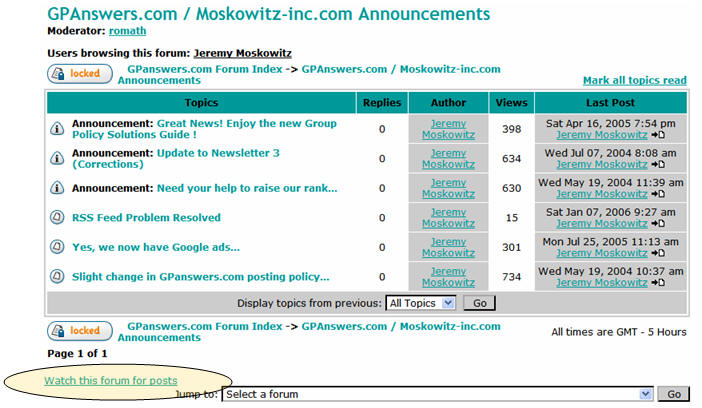 (Click picture to enlarge)
(Click picture to enlarge)
- We're working on a global GPanswers.com search -- which should also be able to buzz through PDFs and all questions in the forums. Not there yet with this one, but stay tuned.
What's new from Microsoft?
Lots, actually! Microsoft has three new documents to help better understand GP. Well, the first one isn't really a "document" but rather a(nother) FAQ for GPOs. Yes, we have one here at GPanswers.com, but I guess it's okay that the boys in Redmond have their own too, right? :-)
Additionally, they released to documents to help understand how Vista and Longhorn will change with Group Policy.
So, how do you find all these new resources? You could Google for hours and not find it! Of course, we have the links, right off ourMicrosoft Resources page. Just scroll to the bottom to check out the new docs.
Subscribe, Unsubscribe, and Usage Information
If you've received this message as a forward from a friend, or are reading it online in the archives, you can sign up for your own newsletter subscription.
Also, if you want to unsubscribe, you can do that, too (but we'll be sad to see you go).
For all Subscription and Unsubscription information, we have a one-stop-shop page at the following address: www.gpanswers.com/newsletter
You can use this information as you see fit, but if you're going to copy any portion, please FORWARD THE ENTIRE email.
While Moskowitz, inc. tries to ensure that all information is technically accurate, we make no warranty with regard to the information within. Please use at your own risk.
If you need personalized attention in any way, just email me: [email protected] If you have questions about ordering a book, contact my assistant Jon at: [email protected] We endeavor to respond to everyone who emails.
Thanks for reading!




Comments (0)