Issue#13
- It's Issue 13 ... Do you feel lucky?
- Technology Takeaway (r), a service of Moskowitz, inc.
- Tips and tricks
- Just one tip: Delegated permissions, the perils therein and how to pull back the reigns
- Tips and tricks
- Get a signed copy of...
- my GP book: Group Policy, Profiles and IntelliMirror
- my Windows & Linux Integration book
- Something new... Two Training Options: Intensive Two day and "Less Intensive Three Day"
- Upcoming Public GP Classes for 2005 / 2006
- What's new around GPanswers.com
- Subscribe, Unsubscribe, and Usage Information
Moskowitz, inc. and www.GPanswers.com -- Issue 13
It wasn't long since the last newsletter, but... when I get busy working on something that affects a lot of people, I want to make sure you get it ASAP!
I think you're really going to like this newsletter. It's HUGE and has *TONS* of graphics for this massive how-to. Don't be scared away by the "unlucky" number 13. Okay, so the big problem we tackle this month is large. The lucky part is that you found this newsletter, and will be well prepared to correct for it!!
After we talk about this, I'll give you an update on my 2006 Group Policy Class Schedule and talk about some other stuff.
Technology Takeaway, a service of Moskowitz, inc.
Delegation... the perils therein, and how to pull back the reigns
One of the key things for your organization to get right is the proper balance of power. Specifically, you need to decide just who creates GPOs and who can link them to areas in Active Directory.
Sometimes, it's just the people in the Domain Admins group. That's fine, if that works for your organization. But if you're the only Domain Administrator, or, if there's only a handful of you, then managing Group Policy for hundreds or thousands of users could be a troubling, cumbersome task which you're always doing again and again. When there's something to be tweaked - you're the one who's called - every time.
Again, if you like it that way - that's great. I'm not proposing to take that away from you. However, if you want some helpers with your GPO comings and goings, then enter the magical world of Group Policy delegation.
The idea is simple: give someone else the rights to create GPOs in the domain, and you won't have to do it. Before you run away and say "My people can't handle this task!!" let's actually analyze this for a second.
First, you need to ask yourself, "Who knows my users best?" Sometimes, that is the Domain Administrator. Sometimes, however, it's the OU administrator, or even, perhaps someone else. We'll call these people (whomever they are) "helper-administrators." For our definition, "helper-administrators" don't have Domain Administrator rights - they're just average Janes and Joes with some ability you've delegated them.
When it comes to Group Policy implementation, one often-successful strategy is to get the power in the hands of the helper-administrators that are closest to the users. So, even though by default, the only people who can create GPOs are Domain Administrators, you might want to re-consider and delegate the permissions such that other administrators (usually OU administrators with non Domain Administrator powers) can also create GPOs.
Delegation 101
In this picture, you can see the basic procedure which permits people the ability to create new GPOs. First, click on the Group Policy Objects node. Then, click on the Delegation tab. Finally, click on Add (at the bottom of the page) and add in the user you want to delegate the ability to create GPOs.
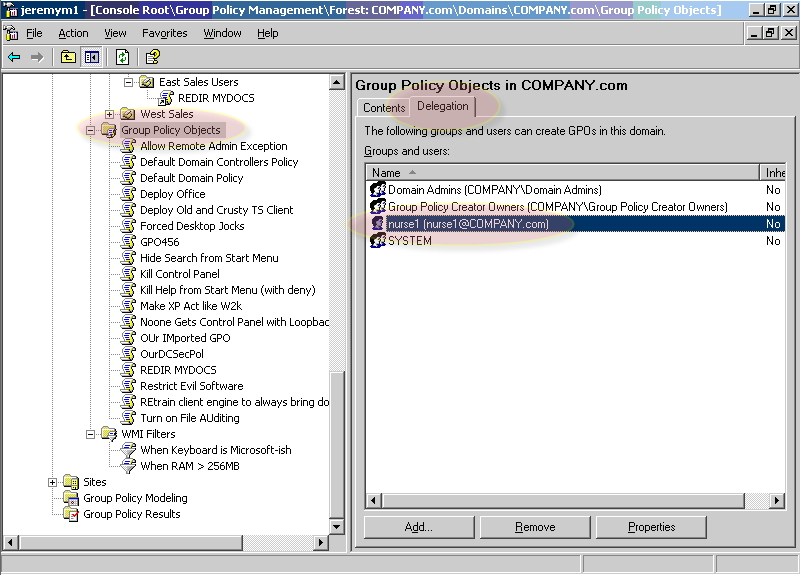
Figure 1: Delegation to create new GPOs occurs at the Group Policy Objects node in the delegation tab (Click on figure to enlarge)
In this example, we'll anoint a helper-administrator, Nurse1 to create GPOs. Now, just because this helper-administrator can create GPOs doesn't mean they can actually do anything useful, like linking them somewhere. In other words, the simple fact that a GPO is createddoesn't inherently mean it's doing anything or affecting anyone. For that, there's another delegation tab, which you'll find at the level in Active Directory you want to delegate (for instance, domain or OU).
In this example, you can see the delegation tab at the Nurses OU.

Figure 2: The Delegation tab at the OU level determines who can link GPOs to this OU (Click on figure to enlarge)
Now that the user Nurse1 can create GPOs, and link them to the Nurses OU, you've empowered this helper-administrator. The idea, again, is that this helper-administrator knows the user population very well, and has the proper knowledge of creating GPOs which (hopefully) won't "break stuff" (to use a technical term.)
However, there are some pitfalls in allowing a helper-administrator to do this. One fear that Domain Administrators (rightly) have is that these delegated helper-administrators can do bad, bad things. This is always a possibility, but then again, you wouldn't delegate someone to drive your Ferrari unless they took a lesson or two, right? (Subtle hint to get your Domain Administrators and OU admins into my highly acclaimed two-day Group Policy Intensive Training and Workshop class, but I digress).
It's very similar here; and as Domain Administrators, sometimes we have issues letting go. :) Let's put aside that specific fear of a helper-administrator messing something up inside a GPO and affecting users, but rather move on to a different sort of problem. The problem of that helper-administrator trying (or inadvertently) "hiding" access of the GPO from the Domain Administrator.
When Good Admins go Bad
Specifically, the person who creates the GPOs also owns the GPO as you can see in this picture.
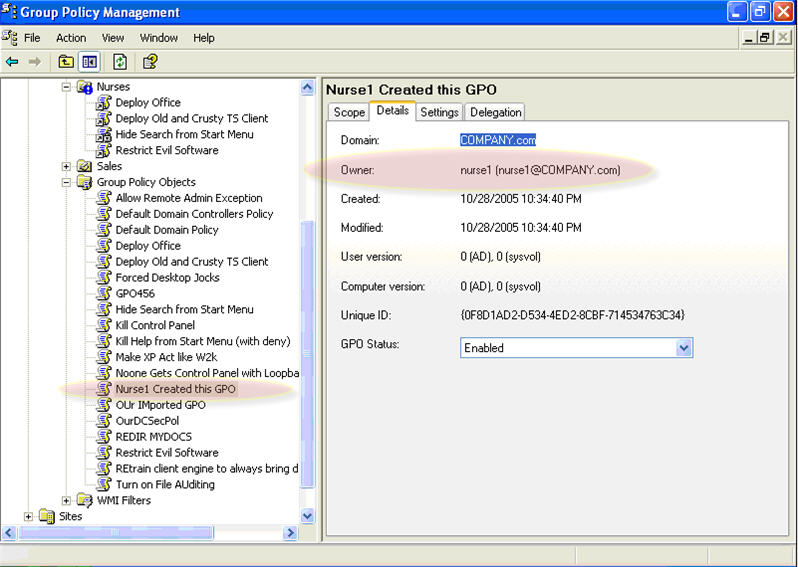
Figure 3: Someone who is delegated the right to create a GPO also owns the GPO (Click on figure to enlarge)
Because the helper-administrator user owns the GPO, they can basically do whatever they want to the GPO. The idea here is that you're granting someone you trust the ability to create GPOs and use them wisely. Hopefully, these helper-administrators will use the power wisely; but, sometimes, administrators are rogues (as Microsoft calls them) or jerks (as I call them).
Rogue-like (or Jerk-like) behavior could include changing the permissions on the GPO so even the Domain Administrator can't see the GPO. In this example, the helper-administrator has set the permissions on the GPO that she has access to as follows:

Figure 4: The helper-administrator has removed permissions from the Domain Administrator with an explicit Deny on all attributes
In other words, the Domain Administrator is Deny-ied access from even seeing the GPO. Now, when the Domain Administrator looks at the Group Policy Objects node in GPMC, the GPO is simply not listed because it is being hiddenby the explicit Deny properties the Nurse put on the GPO.
Note, however, that when Nurse1 linked the GPO to a location in Active Directory the GPO's properties are still viewable though Inaccessible as seen below.
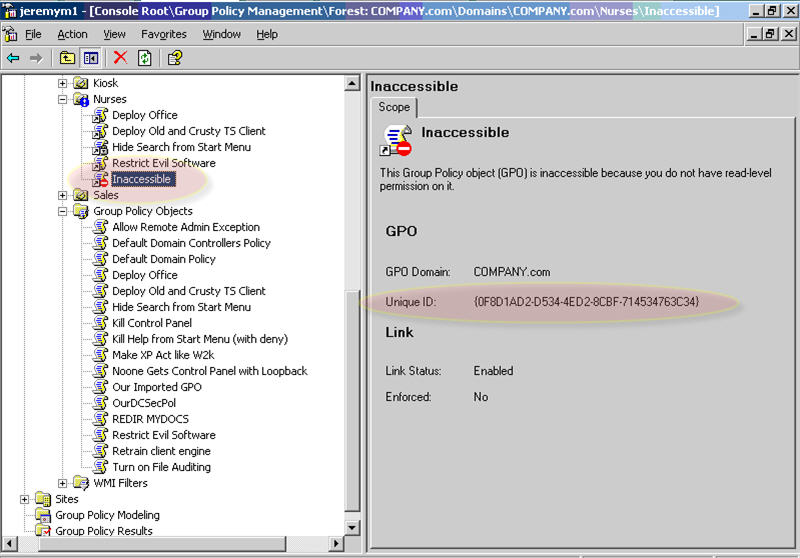
Figure 5: The GPO is now missing from the Group Policy Objects node in the GPMC. However, you can see an Inaccessible marker where it's been linked. (Click on figure to enlarge)
Depending on your perspective, this could be a problem.
On the one hand, the GPO is, in fact, working as advertised and nothing is technically wrong here. The Nurses will get the GPO applied to them and everything will continue functioning normally. The only problem is an unruly helper-administrator who is hiding his or her actions from the Domain Administrator. At this point, you can choose to do two things: nothing, or perform a Take Ownership upon the GPO and put the power back in to your hands.
Reclaiming the Fort: Taking Ownership
Let's examine what it takes to Take Ownership of a GPO as a Domain Administrator and restore the GPO back to health. First, the Group Policy Objects node in the GPMC is a representation of the two halves of a GPO: the GPC (the part that lives in Active Directory) and the GPT (the part that lives in the SYSVOL). In order to perform this, we need to take ownership of both halves.
Let's first examine how to take ownership of the GPC part, because this is the part that controls visibility of the GPO in GPMC.
To do this, we need to go back to the old-school way we used to manage GPOs: Active Directory Users and Computers. To get started, you need to view Advanced Features as seen here in Active Directory Users and Computers.
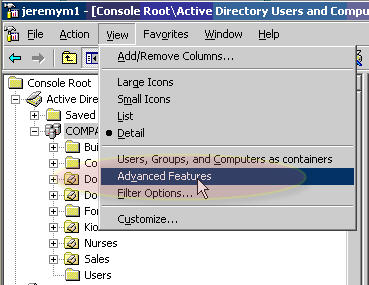
Figure 6: To dive in and see the GPC, we need to enable Advanced Features in Active Directory Users and Computers.
Once Advanced Features is enabled,you can dive down into the GPC part of the Group Policy. You do this by diving into System | Policies and looking for the GUID of the GPO object that currently has the problem. What's interesting in this view is that you cannot see the GUID of the GPO in the left pane, but only in the right pane listed as Unknown.

Figure 7: Inaccessible objects show up in the right pane as Unknown. (Click on figure to enlarge)
When you go to the properties of this object and click the Security tab, you'll see the error message in Figure 8 below.
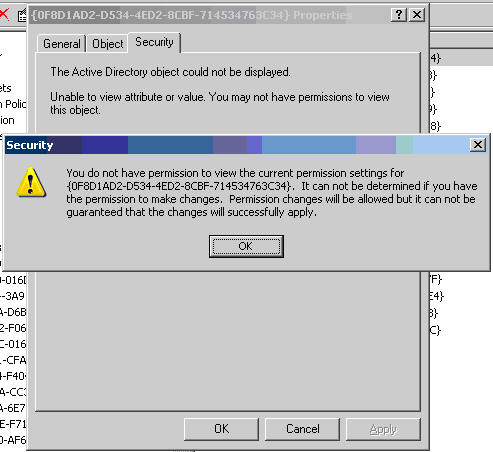
Figure 8: The ACL editor forbids you, the Domain Administrator, from seeing the permissions because you are expressly Denied. (Click on figure to enlarge)
From this point, you might be tempted to give the Domain Administrator, say, Full Control rights. But, if you try it, it won't work. What you really need to do first is to take ownership of the object.
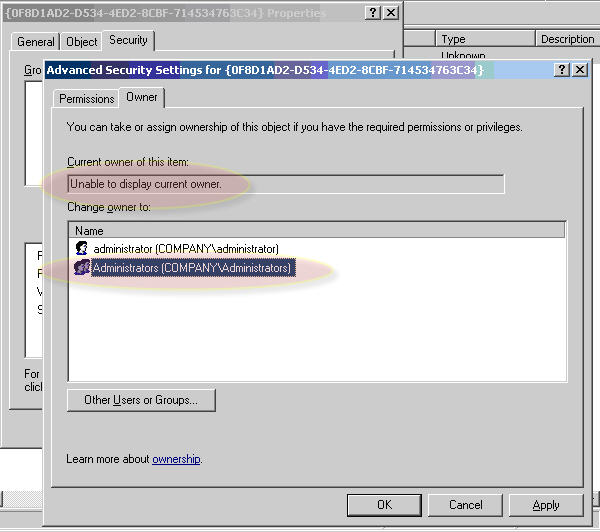
Figure 9: You need to select the Administrators group as the new owner and select Apply. (Click on figure to enlarge)
Unfortunately, once you've taken ownership of the object, you cannot immediately give the proper permissions back to the object. You need to close the ACL editor, and then right-click on the GPC portion again and select Properties | Security. Only now can you actually change the permissions.
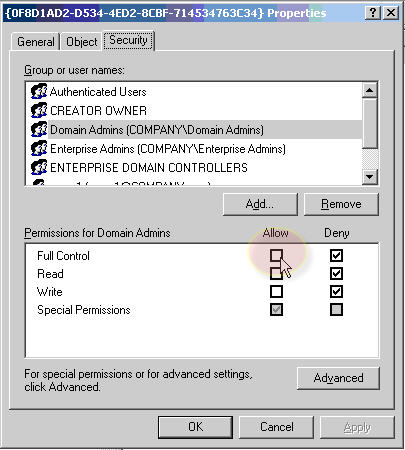
Figure 10: To fix the GPC portion, click Full Control | Allow for the Domain Admins group
Taking Ownership of the GPT
Once you've granted Domain Admins Full Control over the GPC again, you're about halfway finished. Again, all you've fixed is the GPC. Now, it's time to dive into the GPT and perform the same Take Ownership tasks.
The GPT part of a GPO lives on every Domain Controller, typically in the windows system sysvol sysvol {domain-name} policies directory. (Yes, that's two sysvol directories.) Then, inside this directory are directories for each GPO's GPT. In my example here, my GPT has a GUID starting with 0f8D1AD2 (as seen in Figures 7, 8, and 10 among others). So, we need to locate that directory, and take ownership of it in the same way we did with the GPC. You can see this in Figure 11.
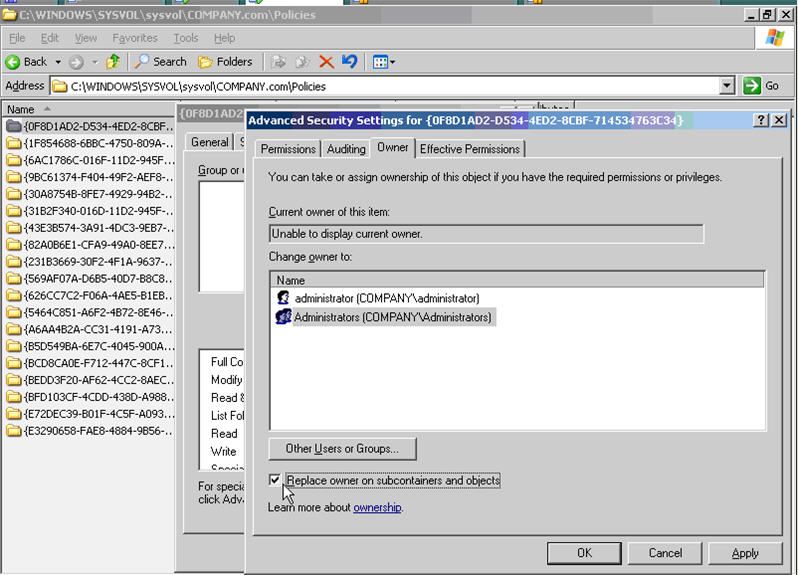
Figure 11: Take ownership of the file-based GPT the same way you did with the Active Directory based GPC (Click on figure to enlarge)
Once performed, you'll have to (again) exit the ACL editor and re-enter it. Then, ensure that Administrators have Full Control similar to the way that you did with the GPC. Though in this case, note that the default permissions should automatically set Administrators (not Domain Admins) to Full Control.
The Final Fixeroo
If you were now to go back to the GPMC and refresh the Group Policy Objects node, you would now see the previously-hidden GPO. However, when you click on it, you might get a message similar to what is seen in Figure 12.
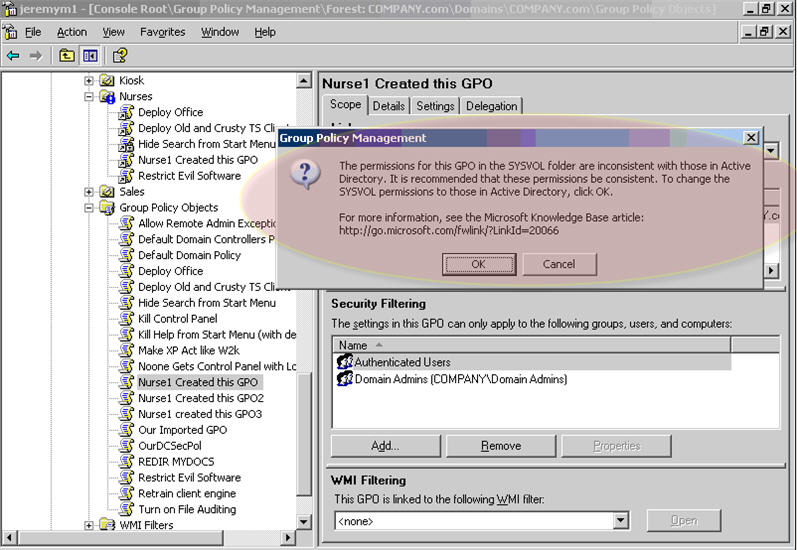
Figure 12: The GPMC recognizes that permissions are amiss between the GPC and GPT. (Click on figure to enlarge)
This is exactly the gift we wanted! Clicking OK will copy the permissions from the GPC over to the GPT. However, the bad news is that you might not actually get this message! If you don't get this message, you have to manually kickstart permissions synchronization between the GPC and GPT.
To do this, click on the Delegation tab of the GPO and click the Advanced button. When you do, you're able to edit the actual ACLs of the GPO, which should (simultaneously) affect both the GPC and GPT. Make a change (any change) and apply it even if it's something temporary. For instance, add a new user and grant that user Read access. Then apply that change. Then, remove that user. The point is to make any change. When you do this, you are writing the ACLs to both the GPC and GPT.
Now they're in sync, and now you've fixed the problem.
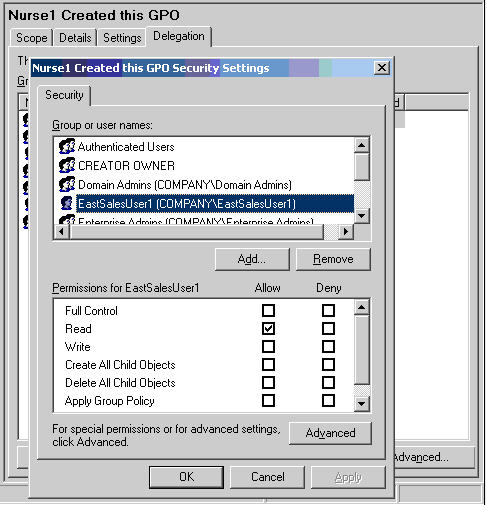
Figure 13: Make a change any change (and apply it). When you do, the GPC and GPT will be simultaneously adjusted to reflect the ACL change. (Click on figure to enlarge)
Moral of the Story
Delegation is a very good thing if you trust the people to whom you're delegating. You can't cover every base, however, and some helper-admins are just going to be jerks. For that reason, this tutorial on how to restore permissions on hidden GPOs will help you know how to take back control.
SPECIAL THANKS to Darren Mar-Elia, CTO for Infrastructure Management Solutions at Quest Software, and operator of GPOguy.com for helping work out this problem with me.
Get signed copies of...
Group Policy, Profiles and IntelliMirror for Windows 2003, Windows XP and Windows 2000 (THIRD EDITION)
-and-
Windows & Linux Integration: Hands on Solutions for a Mixed Environment
Do you have the new THIRD EDITION of the Group Policy book? It's got 50 new pages, fully covers XP/SP2 and Windows Server 2003/SP1, an armload of new tidbits here and there, and whole new section on the Security Configuration Wizard.
Order your signed copy today by clicking here.
Additionally available is my new title Windows & Linux Integration: Hands on Solutions for a Mixed Environment fromwww.WinLinAnswers.com/book.
Oh, and if you own either book, and want to say nice things on Amazon, please do so! That would be great. Thanks! You can do so here:
http://www.amazon.com/gp/product/0782144470 (GPO book)
http://www.amazon.com/gp/product/0782144284 (WinLin book)
Now available: Private GP Course in "Less Intensive" format
Everyone knows the two-day Group Policy course is really three days of material packed in to two intensive days. However, some customers have asked for a "Less Intensive" format.
Your wish has been granted!
This course starts with a half day warm-up of Active Directory, managing users and delegating permissions. Then, we move on to the Group Policy goodies. This way, those with less Group Policy and day-to-day administration can get a bit of fundamentals before diving in to the Group Policy waters.
This "Three-day Less Intensive" option is ONLY available as a private course. Note, the "Two-day intensive" option is available as either a private of public course.
Learn more about the Group Policy courses here.
Public Group Policy Intensive Training and Workshop Schedule Update
I've basically lost count at this point to how many people have signed up and taken the two-day Group Policy Intensive training and workshop. Students LOVE it, and managers LOVE the results the training gives.
You BOUGHT and IMPLEMENTED Active Directory -- now DO SOMETHING with it.
So, learn to properly drive that "Ferrari" you bought by coming to a class!
Classes remaining in 2005:
Dec 13 - 14, 2005: Minneapolis (Bloomington), MN (We almost have enough interested people. If you're interested, or ready to sign up, don't be a stranger! You might be that one person we need to make this class A GO.)
Classes for first half of 2006:
Jan 16 - 17, 2006: Philly / Berwyn, PA (moved from Nov 2005) (We almost have enough interested people. If you're interested, or ready to sign up, don't be a stranger! You might be that one person we need to make this class A GO.)
Jan 24 - 25, 2006: Sacramento, Ca
Jan 26 - 27, 2006: Portland, OR
Feb 21 - 22, 2006: San Antonio (We almost have enough interested people. If you're interested, or ready to sign up, don't be a stranger! You might be that one person we need to make this class A GO.)
Mar 2 - 3, 2006 : Atlanta, GA
Mar 15 - 16, 2006: Washington, DC
Apr 20 - 21, 2006: Oklahoma City, OK
May 15 - 16, 2006: London, England Why THESE cities? Because people used the "Suggest a city" form at https://www.gpanswers.com/suggest and ASKED me to have classes here.
Here's hoping you'll take advantage of the opportunity! Learn more and sign up at: www.gpanswers.com/live-class
(Don't forget to scroll all the way to the bottom of that page and locate your city!)
Or ... if you think you might want your own in-house training of the course (with all the personalized attention that affords), I'd love to join you onsite!
If you have even a handful of in-house people interested in the training, the course pays for itself (as you don't need to ship people offsite!). I'll even travel overseas to the U.K., other parts of Europe, or Japan -- or wherever! Have passport, will travel!
Again, while the training course isn't officially endorsed by Microsoft, the class does the have distinction of being a suggested avenue for intense Group Policy training by members of the Group Policy, Microsoft Consulting Services and Product Support Services teams at Microsoft!
For a public class, sign up online at: www.gpanswers.com/online-class
For a private class, just contact me at [email protected] or call me at 302-351-8408.
Other Changes around GPanswers.com
We've had a mini-web overhaul lately. It might not look a whole lot different, but there's a lot of things, here and there that have been changed.
- There is no more "downloads" section off the main page. The downloads that were there were moved to the FAQ/Tips and Tricks
- Speaking of the FAQ/Tips and Tricks area, the Tips and Tricks are now in categories, which makes things easier to search
- The book downloads (and any updates) are now centrally located right off the main page. It's now called "GP Book Resources"
- We came up with a way to be able to click on any graphic and have it pop-up to full page view. We're working on backfilling all Tips and Tricks, Solutions Guide, and other areas which have scaled-down graphics to enable pop-ups to full size.
- We're working on a global GPanswers.com search -- which should also be able to buzz through PDFs and all questions in the forums. Not there yet with this one, but stay tuned.
Subscribe, Unsubscribe, and Usage Information
If you've received this message as a forward from a friend, or are reading it online in the archives, you can sign up for your own newsletter subscription.
Also, if you want to unsubscribe, you can do that, too (but we'll be sad to see you go).
For all Subscription and Unsubscription information, we have a one-stop-shop page at the following address: www.gpanswers.com/newsletter
You can use this information as you see fit, but if you're going to copy any portion, please FORWARD THE ENTIRE email.
While Moskowitz, inc. tries to ensure that all information is technically accurate, we make no warranty with regard to the information within. Please use at your own risk.
If you need personalized attention in any way, just email me: [email protected] I endeavor to respond to everyone who emails.
Thanks for reading!





Comments (0)