Issue#12
In this issue:
- It's Issue 12 ... Wow.. a new format!
- Group Policy Intensive Training and Workshop Schedule Update for 2006
- Technology Takeaway (r), a service of Moskowitz, inc.
- Juicy tips and tricks (Jumbo sized!)
- All about login scripts (Offline and Online)
- All about WSUS settings
- Juicy tips and tricks (Jumbo sized!)
- Upcoming Conferences, Appearances, and Classes
- Upcoming GP Classes for 2005 and 2006
- Additional Technical Tidbits
- All about VMware's new gizmo and Microsoft's whizbang licensing!
- Get a signed copy of Group Policy, Profiles and IntelliMirror
- Get a signed copy of Windows & Linux Integration
- Subscribe, Unsubscribe, and Usage Information
Moskowitz, inc. and www.GPanswers.com -- Issue 12
This is the first newsletter for a LOT of people I've met in the last several months. I've been to:
- SMB Nation in Seattle
- Two or three Microsoft TS/2 Roadshows
- WinConnections
- TechMentor
- and more !
So, a big hearty WELCOME to all those people who signed up via giving me a business card at an event.
As you can see, our newsletter format has changed a bit. It's now online as a full web page, instead of being a mail-delivered document. Of course, you got the notification via email -- and that's going to stay the same. The good news about putting things in a web page like this is simple: I can inject graphics and other HTML goodies without getting your spam filters all huffy at me.
Let's get right to the goodies, then I'll give you an update on my 2006 Group Policy Class Schedule and talk about some other stuff.
Technology Takeaway (r), a service of Moskowitz, inc.
Here's what's on people's minds recently...
Can logon scripts be set to run when a user re-docks their laptop? (or otherwise force user login script GPO processing via a command or script?)
Scenario: A notebook user can log on to their computer with cached credentials (ie: not connected to the network.) When this happens, it appears that their logon script that maps their drives does not run. Upon returning to the office they dock their computer, but they still do not get their network drives.
So... Can logon scripts be forced to run when the user returns to the office?
The answer in this case is no. Logon GPOs are processed in the foreground, so since they are already logged on using cached credentials, they only get a background refresh, so the logon script settings in this GPO does not run.
This question was submitted recently via email, and it's a good one (so good, we added to the FAQ at www.gpanswers.com/faq).
Is there any advantage to running a login script from the network or from the local PC?
This is something you should consider for laptop users. If you place a script on the local drive of the client and point the GPO to it, the script will run upon logon even if the laptop it is not connected to the network. BUT, it can only perform tasks that don't require the network, so things like mapping network drives won't work.
Oftentimes, administrators choose to perform tasks like mapping network drives and other things which are simply impossible if the network is not available. However, again, technically, the script is trying to run - even if it cannot perform the command you want.
If you have a script that performs some other action that does not depend on the network, login scripts should perform those actions.
How can I configure a workstation to download updates from my WSUS Server (or SUS I haven't upgraded) instead of Windows update?
Windows XP / SP2 comes with the latest "wuau.adm" ADM template which contains the power you need to point your workstation anywhere you want it to retrieve its updates from. The settings are under Computer Configuration | Administrative Templates | Windows Components | Windows Update as seen here.
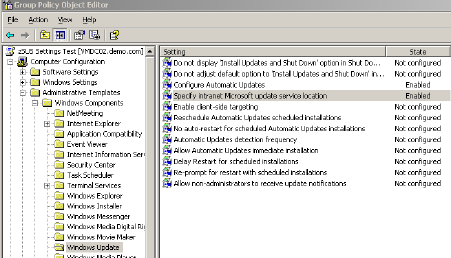
Here you find the following ten settings (a more detailed explanation of each can be found on the settings Explain tab).
- Configure Automatic Updates
This setting must be enabled if you want to specify the settings the workstation needs to retrieve automatic updates using Group Policy. It is essentially the same as using the Control Panel applet to configure the download option, and the installation schedule.
Note there are four potential settings... #2, #3, #4 and #5 as seen below.
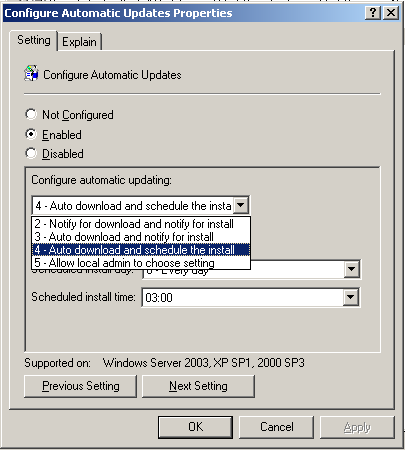
When you set up an OU which contains regular workstations, you'll likely want to set this value to #4 -- which will auto download AND install the patches. This can often mean a reboot, so, be sure to educate your users to SAVE their files before going home for the say.
For the least amount of disruption for your users, you'll want to set your installation to happen off hours, say 3.00 AM.
When you set up an OU which contains SERVERS, you'll likely want to set this value to #3 -- which will auto download, but then notify an administrator who logs on locally to that server that patches have been downloaded. The idea here is that you wouldn't want a server just rebooting at 3.00 AM! You want to control that installation and reboot process a little more closely.
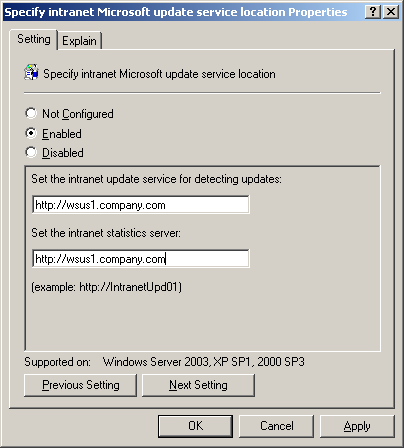
- Specify intranet Microsoft update services location
This setting allows you to point the workstation to the WSUS (or SUS) server in your organization (e.g http://wsus1.company.com). Note that both fields need to point to the same server. It is an invalid configuration to have different entries here.
- Enable client-side targeting
In WSUS, you can create groups for your workstations to belong to. Note that these "groups" aren't NT-style groups. I wish Microsoft had called these "collections" to make the distinction. And, what's more WSUS really doesn't hook in to Active Directory beyond this one setting.
The idea is to have several collections, er, groups then approve specific updates differently as you see fit. For instance, you could have a pilot test group before you roll the update out to everyone. Or, you might manage Doctors differently than Nurses.
The one trick here is that you must first pre-create the groups on the WSUS server. Then, once your client receives this setting you're delivering via Group Policy, they'll automatically find the group.
- Reschedule Automatic Updates scheduled installations
What happens if the workstation is off when it's supposed to be installing your approved patches? In this case, the update will be installed at system startup. This setting allows you to tell the workstation how long to wait after system start before installing the update, and rebooting the workstation.
Be careful not to have the computer wait too long after startup, as your users may start working away and all of the sudden their machine says is about to reboot. Chances are, your user will turn on their computer before they grab their morning coffee, so if you can set the delay to less then five minutes, chances are they wonât even notice!
- No auto-restart for scheduled Automatic Updates installations
If you have âReschedule Automatic Updates scheduled installationsâ setting enabled, you can also enable this setting if you do not want the computer to automatically reboot after the installation. The user will be notified that a reboot is required to complete the installation.
- Automatic Updates detection frequency
You can tell the workstation how often it should check in with the Update Server by enabling this setting. The detection frequency is the hours specified, minus zero to 20 percent of the hours specified. The default setting 22 hours.
- Allow Automatic Updates immediate installation
If an update that is approved can be installed without interrupting Windows service and does not restart Windows, it will be installed immediately upon detection if this setting is enabled.
Although an update like this has yet to have been seen, itâs a nice idea, to have the update apply as soon as possible.
- Delay Restart for scheduled installations
By default, Windows will wait five minutes after installation before rebooting the computer. This setting allows you to specify how many minutes the computer should wait before reboot.
- Re-prompt for restart with scheduled installations
This setting allows you to set the amount of time that passes before re-prompting that a restart is required to complete an installation of updates.
If you are automatically installing updates and restarting machines after hours, this setting isnât necessary.
- Allow non-administrators to receive update notifications
Enabling this setting will allow non-administrators to receive notifications either before downloading or before installation of updates.
Again, If you are setting your computers to install and restart during off hours, this setting isnât necessary, unless you really want your users to install the updates and restart their computers during the workday.
Group Policy Intensive Training and Workshop Schedule Update
I've basically lost count at this point to how many people have signed up and taken the two-day Group Policy Intensive training and workshop. Students LOVE it, and managers LOVE the results the training gives.
You BOUGHT and IMPLEMENTED Active Directory -- now DO SOMETHING with it.
So, learn to properly drive that "Ferrari" you bought by coming to a class!
Classes remaining in 2005:
Nov 28 - 29, 2005: Philadelphia (Berwyn, PA)
(We almost have enough interested people. If you're interested, or ready to sign up, don't be a stranger! You might be that one person we need to make this class A GO.)
Dec 13 - 14, 2005: Minneapolis (Bloomington), MN
(We almost have enough interested people. If you're interested, or ready to sign up, don't be a stranger! You might be that one person we need to make this class A GO.)
Classes for first half of 2006:
Jan 24 - 25, 2006: Sacramento, Ca
Jan 26 - 27, 2006: Portland, OR
Feb 21 - 22, 2006: San Antonio
(We almost have enough interested people. If you're interested, or ready to sign up, don't be a stranger! You might be that one person we need to make this class A GO.)
Mar 2 - 3, 2006 : Atlanta, GA
Mar 15 - 16, 2006: Washington, DC
Apr 20 - 21, 2006: Oklahoma City, OK
May 15 - 16, 2006: London, England
Why THESE cities? Because people used the "Suggest a city" form at https://www.gpanswers.com/suggest and ASKED me to have classes here.
Here's hoping you'll take advantage of the opportunity!
Learn more and sign up at: https://www.gpanswers.com/workshop
(Don't forget to scroll all the way to the bottom of that page and locate your city!)
Or ... if you think you might want your own in-house training of the course (with all the personalized attention that affords), I'd love to join you onsite!
If you have even a handful of in-house people interested in the training, the course pays for itself (as you don't need to ship people offsite!). I'll even travel overseas to the U.K., other parts of Europe, or Japan -- or wherever! Have passport, will travel!
Again, while the training course isn't officially endorsed by Microsoft, the class does the have distinction of being a suggested avenue for intense Group Policy training by members of the Group Policy, Microsoft Consulting Services and Product Support Services teams at Microsoft!
For a public class, sign up online at: https://www.gpanswers.com/workshop/
For a private class, just contact me at [email protected] or call me at 302-351-8408.
Additional technical tidbits...
Even though the thoughts in this section aren't necessarily Group Policy related, I thought these tidbits might be something you all would find interesting.
Tidbit #1: Microsoft gets really generous with virtualization licensing Microsoft has a new press release regarding their upcoming virtualization strategy here: http://tinyurl.com/c78kf
There's a lot here, but there's one key sentence which rocked my world (and I quote):
"Licenses for the upcoming Windows Server 2003 R2 Enterprise Edition will allow customers to run up to four virtual instances on one physical server at no additional cost..."
And, this licensing deal is also expected to carry through to Longhorn (Enterprise) Server as well.
In a word: WOW. This means that if you buy one copy of Enterprise server, and you run it virtually, you basically get 4 copies of Enterprise server for the price of one! Now, of course, the key word here is "Enterprise." This is the more (much more) expensive version of Windows Server. Note that Windows Standard server (the less expensive sibling) is left out in the cold here.
The other issue is... is this deal only good when you use Microsoft's Virtualization technology (Virtual PC or Virtual Server?) In other words, if a shop chooses to use VMware as their virtualization platform, does the deal hold up? Well, there's nothing here in this press release which specifically says you can't use VMware if you wanted -- which is good news. However, before rolling out a bazillion (free) copies of Windows R2 Enterprise Server, be sure to consult with your licensing mavens, just to be sure.
Tidbit #2: VMware gets really generous with free virtualization technology!
Rumors have it that Windows Vista will have a free free free built-in version of Microsoft Virtual PC. There will be a small restriction on it, though: you can only have ONE running virtual-machine at a time. I think when VMware heard this upcoming plan, they got a little nervous, and came out with {insert fanfare music here} the VMware Player. The VMware Player takes existing VMware virtual-machines and allows you to, you guessed it -- use them for free anywhere you like. And you're not limited to just ONE running virtual-machine. So, in short, if you've already CREATED your virtual-machine with, say, VMware Workstation or VMWare GSX server -- just copy the files to a friend, give him or her the free VMware Player application -- and -- they're running your virtual-machine! Way to go VMware! It's in beta (thought it looks like production quality software to me.) You can download it here. Again, the only thing you really CANNOT do in VMware Player is CREATE new virtual-machines. Other than that -- it's quite similr to VMware Workstation.
Get signed copies of...
Group Policy, Profiles and IntelliMirror for Windows 2003, Windows XP and Windows 2000 (THIRD EDITION)
-and-
Windows & Linux Integration: Hands on Solutions for a Mixed Environment
Do you have the new THIRD EDITION of the Group Policy book? It's got 50 new pages, fully covers XP/SP2 and Windows Server 2003/SP1, an armload of new tidbits here and there, and whole new section on the Security Configuration Wizard.
Order your signed copy today by clicking here: https://www.gpanswers.com/book/
Additionally available is my new title Windows & Linux Integration: Hands on Solutions for a Mixed Environment from www.WinLinAnswers.com/book.
Oh, and if you own either book, and want to say nice things on Amazon, please do so! That would be great. Thanks! You can do so here:
http://www.amazon.com/gp/product/0782144470 (GPO book)
http://www.amazon.com/gp/product/0782144284 (WinLin book)
New Forum in the GPanswers.com/community
Want to have an ongoing discussion about anything in this newsletter? Then head on over tohttps://www.gpanswers.com/community/viewforum.php?f=33
where you can talk with your peers about anything in this newsletter (or previous ones!) Be sure to use the newsletter number when you post!
Subscribe, Unsubscribe, and Usage Information
If you've received this message as a forward from a friend, or are reading it online in the archives, you can sign up for your own newsletter subscription.
Also, if you want to unsubscribe, you can do that, too (but we'll be sad to see you go).
For all Subscription and Unsubscription information, we have a one-stop-shop page at the following address: www.gpanswers.com/newsletter
You can use this information as you see fit, but if you're going to copy any portion, please FORWARD THE ENTIRE email.
While Moskowitz, inc. tries to ensure that all information is technically accurate, we make no warranty with regard to the information within. Please use at your own risk.
If you need personalized attention in any way, just email me: [email protected] I endeavor to respond to everyone who emails.
Thanks for reading!




Comments (0)